According to Zimperium analysts, Iranian hackers use the new RatMilad spyware targeted at Android users in their attacks. The malware is used both to spy on victims and to steal their data.
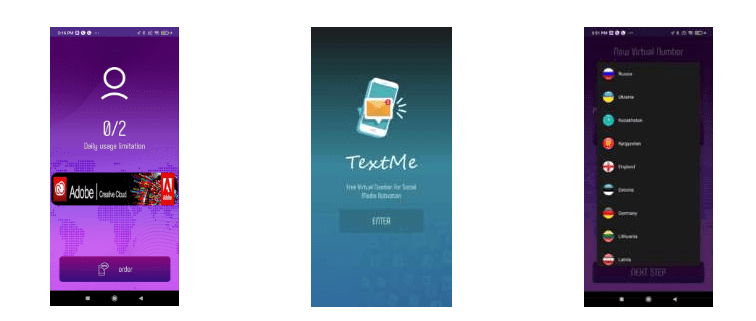
The malware is being distributed under the guise of VPN applications, as well as fake virtual number generators NumRent and Text Me, which can allegedly be used to activate social media accounts. During installation, the application asks for a lot of permissions and then abuses them to download the malicious RatMilad payload.
Basically, attackers distribute their fake apps through Telegram, as they are not available in the Google Play Store and third-party stores. For example, the researchers found a Telegram channel in which a message with a link to a malicious application received more than 4,700 views and was forwarded over 200 times.
In addition, the operators of this campaign have created a special site advertising NumRent to make the application look more convincing. This site is promoted through ads on Telegram as well as social media and other communication platforms.
Having penetrated the victim’s device, RatMilad begins to collect information. The wide range of permissions requested by the malware allows access to device data (including MAC address, SIM card data, and exact location) and user information (for example, contacts, call logs, SMS messages, clipboard data, multimedia, and files).
Also, attackers can perform actions with files, change the permissions of installed applications, and gain access to the camera and microphone of an infected device in order to record video and audio, as well as take photos.
The researchers believe that the attackers behind this campaign received the source code of the malware from the AppMilad hacker group, after which they integrated it into their fake applications. Apparently, RatMilad is not a targeted campaign, and in this case, the victims of hackers are not specific targets, but completely random users.